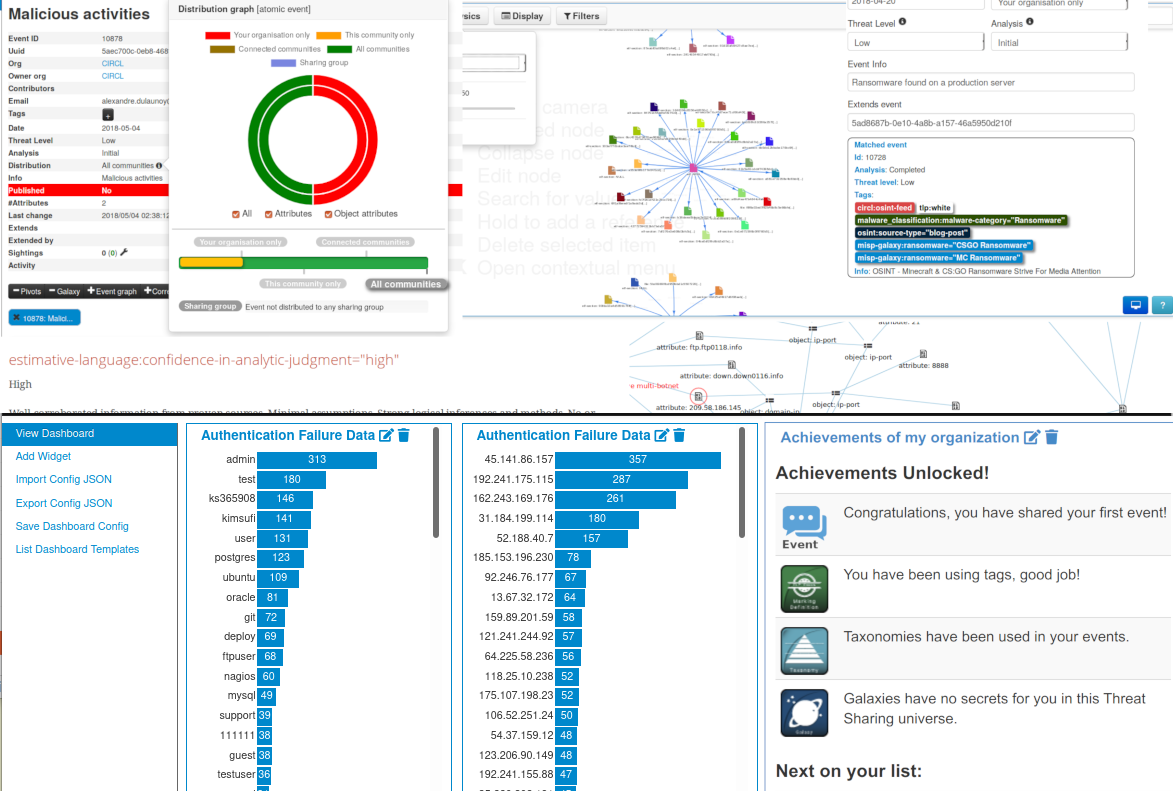
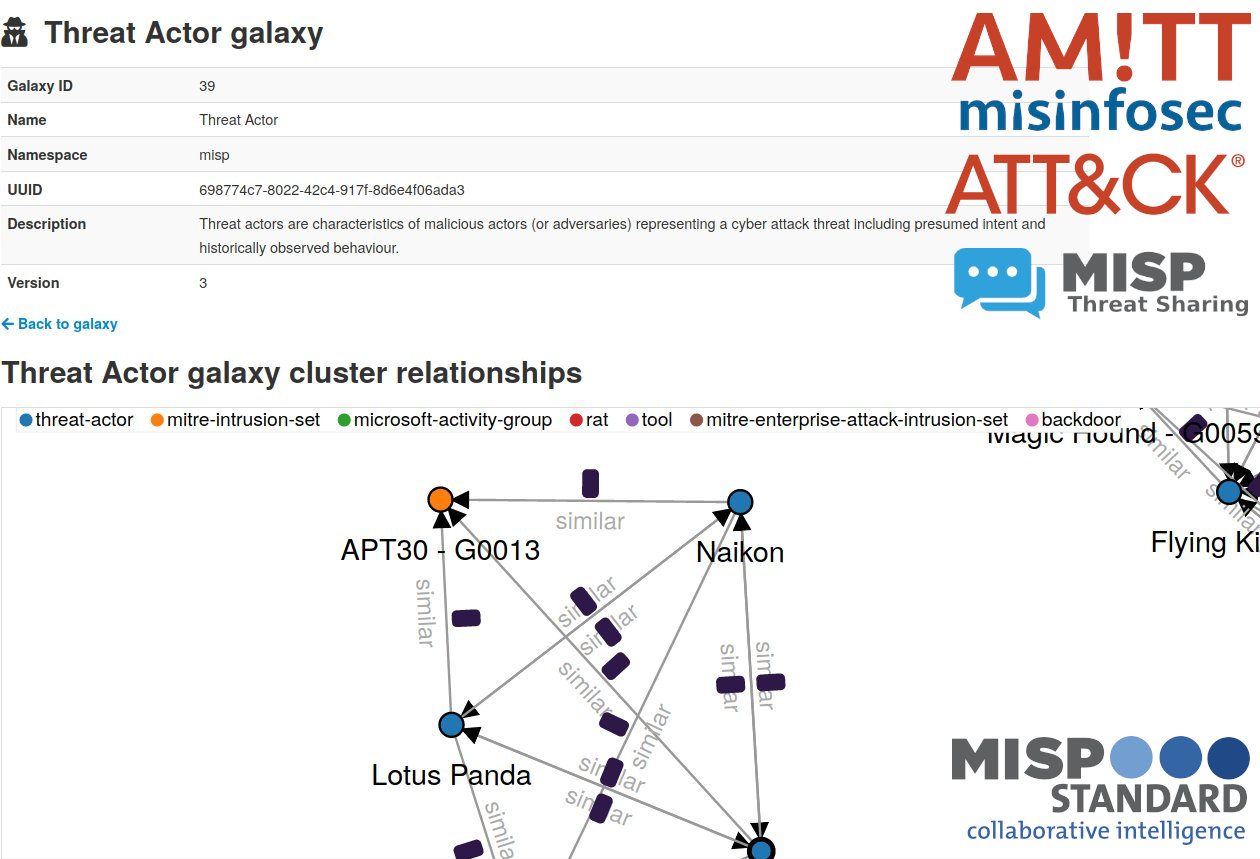
The MISP is an open source software solution for collecting, storing, distributing and sharing cyber security indicators and threats about cyber security incidents analysis and malware analysis. MISP is designed by and for incident analysts, security and ICT professionals or malware reversers to support their day-to-day operations to share structured information efficiently.
MISP 2.4.213 & 2.5.15 Released - A Double Dose of Security, Search, and Stability
We are thrilled to announce a dual release of MISP, bringing significant enhancements to both our stable and development branches with versions 2.4.213 and 2.5.15.